Because Security Gives Us Freedom.
Protect Your Network & Get Cybersecurity Compliant
Our purpose is to give you the freedom to move at the speed of business without worrying about cybersecurity.
We keep you from falling into the Cybersecurity Technology Trap: you need more than just technology to protect your network. Cybersecurity is a process, not a product.
Managed Security Services:
Our Elite Blue Team Will Defend Your Network 24/7
Protect Customer Data
Protect your network against threats with 24/7 security orchestration, including SIEM, MDR and rapid response to mitigate potential cybersecurity issues.
Keep Regulators Happy
Get cybersecurity compliant with government and industry requirements, including FDIC, FFIEC, GLBA, HIPAA, PCI, and more.
Give Your Board Confidence
Answer “What are you doing about cybersecurity?” with total confidence knowing you’ve got all the reporting you need for board members to feel secure.

Empower Your IT Team
Extend your IT department's capabilities to ensure network security, diagnose real threats vs. false positives, and keep up with best practices and technology.
How We Work
Panoptic Cyberdefense®
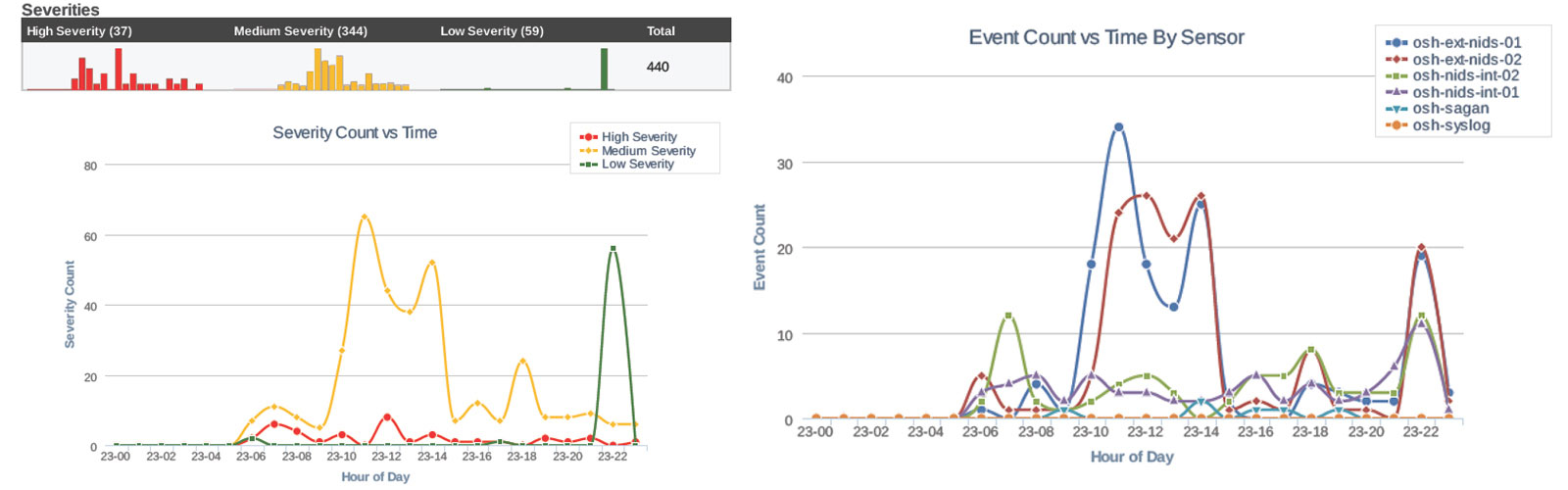
Our core service is our 24/7 SOC-as-a-Service with MDR, NDR, and Security Orchestration augmenting your team.
onShore clients sleep well at night because they trust us to protect their network as a 24/7 security operations center (SOC), complete with reporting to prove that we’re doing what we promise.
We call this Panoptic Cyberdefense managed security services, which includes:
- Managed Detection & Response (MDR)
- MDR + Network Detection and Response
- Security Orchestration
Managed Security Solutions
We don’t stop there. We fully supply and manage systems such as NexGen Firewalls, EDR, MFA, and Vulnerability Management for protection and compliance.
Using cutting edge technology is central to protecting your network and getting you compliant – and so is monitoring, tuning and reporting on its findings.
We supply, monitor and support a wide variety of technology, including:
- Panoptic Sensors & SIEM
- Managed NexGen Firewalls
- Managed EDR
- Vulnerability Management
- Email Security
- SD-WAN
Cybersecurity Leadership
Our consulting helps you develop your true security posture and program. Proceed confidently with the support of your executive team and board.
Are you concerned about intrusions, ransomware, business email compromise (BEC), or other critical gaps in your cybersecurity?
If so, get a Cybersecurity Check-Up today or learn more about our other cybersecurity assessments:
- Dark Web Monitoring: get a free scan today
- Risk Assessments
- Cybersecurity Policy Creation
- Governance, Risk & Compliance (GRC) Consulting
- vCISO Outsourcing